Menu
December 29, 2014: Various and sundries
ID'ed by your body cam: If you wear a video camera, you can be identified based on only four seconds of the video recorded by the camera. A research paper entitled "Egocentric Video Biometrics" makes that claim, although it must be noted that the paper was not subjected to peer review. Ars Technica's Marek Ziolkowski reports on the research in a December 15, 2014, article.
Financial industry looks to government for cybersecurity guidance: The outlook appears bright for the Cybersecurity Information Sharing Act, which Congress intends as the framework for collecting and sharing "cyber threat information," as Michael Dodson describes it in a December 15, 2014, post on the JD Supra site. Financial services in particular are hoping the law will provide guidance on what constitutes adequate protections to reduce their liability for data breaches that put their customers at risk.
Courts are increasingly finding that heightened risk of future damage is sufficient grounds for a cause of action against an entity that suffers a data breach after failing to implement adequate security precautions. If the organization can show that it complied with government cybersecurity guidelines, it may be able to avoid liability in the event of a breach of its networks. At present, there are no such guidelines.
Dodson cites several cases in which financial companies had reason to believe their networks were at risk and failed to act, which made them liable for potential damages to plaintiffs whose data was lost. In the past, courts generally required a showing of actual damages to plaintiffs as a result of data breaches. Those days appear to be coming to an end, which increases the need for such guidelines by any entity that collects and stores anyone's personal information.
Yahoo does a 180 on use of Creative Commons images: The December 16, 2014, Weekly explained how Yahoo intended to profit via its Wall Art print service from use of Flickr images that were assigned a Creative Commons license when they were uploaded to the service (see below). In a December 18, 2014, article, TechCrunch's Catherin Shu reports that Yahoo has subsequently removed Creative Commons-licensed images from the service. The company also stated that it would refund all sales of such images.
As I stated in the original post, not all of the affected CC licensees objected to the use of their images by the service. They were happy to receive the increased exposure for their pictures and expected no monetary compensation. There was also nothing illegal about Yahoo's use of the CC-licensed images. But Yahoo decided to take a step back and consult with the community before proceeding with its plans. To that I say, "Yippee!"
Financial industry looks to government for cybersecurity guidance: The outlook appears bright for the Cybersecurity Information Sharing Act, which Congress intends as the framework for collecting and sharing "cyber threat information," as Michael Dodson describes it in a December 15, 2014, post on the JD Supra site. Financial services in particular are hoping the law will provide guidance on what constitutes adequate protections to reduce their liability for data breaches that put their customers at risk.
Courts are increasingly finding that heightened risk of future damage is sufficient grounds for a cause of action against an entity that suffers a data breach after failing to implement adequate security precautions. If the organization can show that it complied with government cybersecurity guidelines, it may be able to avoid liability in the event of a breach of its networks. At present, there are no such guidelines.
Dodson cites several cases in which financial companies had reason to believe their networks were at risk and failed to act, which made them liable for potential damages to plaintiffs whose data was lost. In the past, courts generally required a showing of actual damages to plaintiffs as a result of data breaches. Those days appear to be coming to an end, which increases the need for such guidelines by any entity that collects and stores anyone's personal information.
Yahoo does a 180 on use of Creative Commons images: The December 16, 2014, Weekly explained how Yahoo intended to profit via its Wall Art print service from use of Flickr images that were assigned a Creative Commons license when they were uploaded to the service (see below). In a December 18, 2014, article, TechCrunch's Catherin Shu reports that Yahoo has subsequently removed Creative Commons-licensed images from the service. The company also stated that it would refund all sales of such images.
As I stated in the original post, not all of the affected CC licensees objected to the use of their images by the service. They were happy to receive the increased exposure for their pictures and expected no monetary compensation. There was also nothing illegal about Yahoo's use of the CC-licensed images. But Yahoo decided to take a step back and consult with the community before proceeding with its plans. To that I say, "Yippee!"
December 16, 2014: Cyberwar? Fuhgeddabouddit!

There are plenty more serious threats worth fretting over, such as your everyday, ordinary Internet thievery, which is now the most-common property crime in the U.S., totaling $24 billion in losses in 2012.
December 16, 2014: Yahoo cashes in on your cute, royalty-free Flickr images
Millions of people have uploaded billions of images to Yahoo's Flickr image-sharing service. Not many of the uploaders expect any payment from people who download or otherwise use their images. In a December 10, 2014, post on the Sophos Naked Security blog, Lisa Vaas explains that Yahoo is planning to make canvas prints from 50 million Flickr images that have Creative Commons licenses. The prints will be sold for up to $49 each, according to Vaas.
The company will also use images for the prints whose creators have retained the licensing rights to; these people will receive a 51-percent share of the sales proceeds. The CC licensees are out of luck -- and there's nothing illegal about it.
Not all the people whose CC-licensed images will be used object to the lack of any payment, however. Many are satisfied with the extra exposure the prints will afford them. If you're a Flickr user who would like to retain the rights to your images, you can change the license type by opening your Albums and choosing "Batch edit > Change licensing." Your licensing options are shown in the image above.
As Vaas points out, for people who've uploaded thousands of CC-licensed images to the service, there's no practical way to opt out of Yahoo's sale and unfettered reuse of the pictures. The lesson is to be careful about which Internet services you trust with your data. Once a file is in the cloud, you've ceded a goodly amount of control over it, one way or the other.
Could external hard drives be making a comeback? Nah, but maybe a new kind of cloud-storage service is needed -- one such as SpiderOak that lets you encrypt your data before you upload it so that only you can decrypt it.
The company will also use images for the prints whose creators have retained the licensing rights to; these people will receive a 51-percent share of the sales proceeds. The CC licensees are out of luck -- and there's nothing illegal about it.
Not all the people whose CC-licensed images will be used object to the lack of any payment, however. Many are satisfied with the extra exposure the prints will afford them. If you're a Flickr user who would like to retain the rights to your images, you can change the license type by opening your Albums and choosing "Batch edit > Change licensing." Your licensing options are shown in the image above.
As Vaas points out, for people who've uploaded thousands of CC-licensed images to the service, there's no practical way to opt out of Yahoo's sale and unfettered reuse of the pictures. The lesson is to be careful about which Internet services you trust with your data. Once a file is in the cloud, you've ceded a goodly amount of control over it, one way or the other.
Could external hard drives be making a comeback? Nah, but maybe a new kind of cloud-storage service is needed -- one such as SpiderOak that lets you encrypt your data before you upload it so that only you can decrypt it.
December 9, 2014: Five fantastic Web freebies

There has never been a better time to be a cheapskate. The Internet is full of free programs and services, not to mention public-domain books, pictures, videos, and music available royalty-free. Here's a quick look at five of my favorite freebies.
December 9, 2014: Internet privacy awareness is on the upswing, and a common-sense drug policy articulated by a state court
New tools tell you what the trackers and snoops know about you
Want to get creeped out? Use one of the many programs that tell you what personal information social media and other Web sites have collected about you: Creepy, PleaseRobMe.com, and Girls Around Me, which is a service that locates pictures of women who are near you and superimposes the pictures onto a map.
There are also apps that scan social-media posts in an attempt to identify people who are suicidal; others track your movements through a store; and one called Turnstyle even follows you around the city of Toronto.
The Guardian's Ben Goldacre explains in a December 5, 2014, article that nearly all security is now digital, but we don't understand how it works. Instead, we are dealing with "a series of black boxes into which we entrust our money, our privacy and everything else we might hope to have under lock and key. We have no clear sight into this world, and we have few sound intuitions into what is safe and what is flimsy – let alone what is ethical and what is creepy. We are left operating on blind, ignorant, misplaced trust; meanwhile, all around us, without our even noticing, choices are being made."
Two areas in particular where reams of sensitive data are being collected are health and finance. Imagine your refrigerator reporting to your insurance company on your excessive ice cream intake. Or merchants basing the price you pay for their goods and services on what they know about how badly you need the product, or how willing you would be to overpay (whether you know you're overpaying or not.)
Now imagine the market intelligence in the hands of consumers, who can determine more precisely the market value of an item right here, right now, and can time their purchases accordingly. Which way do you think the information-distribution pendulum will swing?
-----------------------------------------------------------
There's a reason why Internet services don't talk about privacy
People on the Internet are increasingly concerned about losing their privacy. That's according to the results of a recent Pew Research Internet Project survey. The Pew numbers, which were released on November 12, 2014, indicate that 91 percent of U.S. adults agree or strongly agree that consumers have lost control of the collection and use of their personal information by companies.
The results of another Pew survey, released on December 4, 2014, show that more than half of us erroneously believe that a Web site's privacy policy ensures the company keeps confidential all information it collects about its customers. In fact, they should be called anti-privacy policies because they grant the company the right to use whatever information it collects about you in nearly any way it chooses.
In any event, few people bother reading privacy policies, which isn't a surprise, considering that Joseph Turow of the University of Pennsylvania Annenberg School Communications calls the policies "unreadable."
Forbes' Jonathan Salem Baskin writes in a December 7, 2014, article that people may not know much about what's happening with their personal information now, but it won't take long for them to realize there's an "asymmetrical exchange of information" going on, and consumers are getting the short end of the stick. Baskin hints that some of the more forward-thinking of the multibillion-dollar behemoths might want to get ahead of this trend before the inevitable consumer backlash swamps them.
------------------------------------------------------------------
Common-sense drug policy from courts in the Land of the Midnight Sun
In 1975, the Alaska Supreme Court ruled that the state's Constitutional right to privacy prevented law enforcement from preventing people from smoking marijuana in their own homes. The state would need a "compelling interest" to violate the person's privacy, not the lower threshold of an interest that is merely "rationally related[] to the accomplishment of a permissible state policy."
The state argued that the health and safety of its citizens outweighed the privacy rights of individuals who wanted to smoke marijuana in their homes. The court disagreed, ruling that marijuana use "does not constitute a public health problem of any significant dimensions. It is, for instance, far more innocuous in terms of physiological and social damage than alcohol or tobacco.”
In 1978, the Alaska Supreme Court revisited the issue, this time as it related to cocaine use. In this instance, the court ruled that cocaine is far more dangerous than marijuana, in part because you can die of an overdose. Therefore, the state's argument that it must protect the health and safety of citizens justifies the violation of the constitutional right to privacy. The police can arrest you for using cocaine in your home.
Fast-forward to 1984, when the issue came up again in relation to alcohol use. Some local communities had taken advantage of a 1981 Alaska statute that allowed them to ban alcohol, although people could still drink alcoholic beverages in their homes. A man was convicted of importing alcohol to one such community in violation of the ordinance. The man argued that the conviction violated his constitutional right to privacy. The court ruled that alcohol was more like cocaine than marijuana in terms of its threat to the community's health and safety.
Last month, Alaskans approved the sale and use of marijuana in the state. Some communities want to include marijuana in their local prohibition of alcohol. Even if the legislature (or the state courts) allow marijuana to be prohibited in local communities that decide to do so, it appears people in those areas would retain a constitutional right to use the drug in their own homes.
As AlterNet's David Morris states in a December 4, 2014, article, the Alaska courts are to be commended for using "scientific evidence to determine the balance between the right of the state to protect its citizens with the right of its citizens to be left alone. The U.S. Congress and Supreme Court have much to learn from the next to last state to join the Union."
Want to get creeped out? Use one of the many programs that tell you what personal information social media and other Web sites have collected about you: Creepy, PleaseRobMe.com, and Girls Around Me, which is a service that locates pictures of women who are near you and superimposes the pictures onto a map.
There are also apps that scan social-media posts in an attempt to identify people who are suicidal; others track your movements through a store; and one called Turnstyle even follows you around the city of Toronto.
The Guardian's Ben Goldacre explains in a December 5, 2014, article that nearly all security is now digital, but we don't understand how it works. Instead, we are dealing with "a series of black boxes into which we entrust our money, our privacy and everything else we might hope to have under lock and key. We have no clear sight into this world, and we have few sound intuitions into what is safe and what is flimsy – let alone what is ethical and what is creepy. We are left operating on blind, ignorant, misplaced trust; meanwhile, all around us, without our even noticing, choices are being made."
Two areas in particular where reams of sensitive data are being collected are health and finance. Imagine your refrigerator reporting to your insurance company on your excessive ice cream intake. Or merchants basing the price you pay for their goods and services on what they know about how badly you need the product, or how willing you would be to overpay (whether you know you're overpaying or not.)
Now imagine the market intelligence in the hands of consumers, who can determine more precisely the market value of an item right here, right now, and can time their purchases accordingly. Which way do you think the information-distribution pendulum will swing?
-----------------------------------------------------------
There's a reason why Internet services don't talk about privacy
People on the Internet are increasingly concerned about losing their privacy. That's according to the results of a recent Pew Research Internet Project survey. The Pew numbers, which were released on November 12, 2014, indicate that 91 percent of U.S. adults agree or strongly agree that consumers have lost control of the collection and use of their personal information by companies.
The results of another Pew survey, released on December 4, 2014, show that more than half of us erroneously believe that a Web site's privacy policy ensures the company keeps confidential all information it collects about its customers. In fact, they should be called anti-privacy policies because they grant the company the right to use whatever information it collects about you in nearly any way it chooses.
In any event, few people bother reading privacy policies, which isn't a surprise, considering that Joseph Turow of the University of Pennsylvania Annenberg School Communications calls the policies "unreadable."
Forbes' Jonathan Salem Baskin writes in a December 7, 2014, article that people may not know much about what's happening with their personal information now, but it won't take long for them to realize there's an "asymmetrical exchange of information" going on, and consumers are getting the short end of the stick. Baskin hints that some of the more forward-thinking of the multibillion-dollar behemoths might want to get ahead of this trend before the inevitable consumer backlash swamps them.
------------------------------------------------------------------
Common-sense drug policy from courts in the Land of the Midnight Sun
In 1975, the Alaska Supreme Court ruled that the state's Constitutional right to privacy prevented law enforcement from preventing people from smoking marijuana in their own homes. The state would need a "compelling interest" to violate the person's privacy, not the lower threshold of an interest that is merely "rationally related[] to the accomplishment of a permissible state policy."
The state argued that the health and safety of its citizens outweighed the privacy rights of individuals who wanted to smoke marijuana in their homes. The court disagreed, ruling that marijuana use "does not constitute a public health problem of any significant dimensions. It is, for instance, far more innocuous in terms of physiological and social damage than alcohol or tobacco.”
In 1978, the Alaska Supreme Court revisited the issue, this time as it related to cocaine use. In this instance, the court ruled that cocaine is far more dangerous than marijuana, in part because you can die of an overdose. Therefore, the state's argument that it must protect the health and safety of citizens justifies the violation of the constitutional right to privacy. The police can arrest you for using cocaine in your home.
Fast-forward to 1984, when the issue came up again in relation to alcohol use. Some local communities had taken advantage of a 1981 Alaska statute that allowed them to ban alcohol, although people could still drink alcoholic beverages in their homes. A man was convicted of importing alcohol to one such community in violation of the ordinance. The man argued that the conviction violated his constitutional right to privacy. The court ruled that alcohol was more like cocaine than marijuana in terms of its threat to the community's health and safety.
Last month, Alaskans approved the sale and use of marijuana in the state. Some communities want to include marijuana in their local prohibition of alcohol. Even if the legislature (or the state courts) allow marijuana to be prohibited in local communities that decide to do so, it appears people in those areas would retain a constitutional right to use the drug in their own homes.
As AlterNet's David Morris states in a December 4, 2014, article, the Alaska courts are to be commended for using "scientific evidence to determine the balance between the right of the state to protect its citizens with the right of its citizens to be left alone. The U.S. Congress and Supreme Court have much to learn from the next to last state to join the Union."
December 2, 2014: How Google, Facebook, and Twitter make billions by offering 'free' services
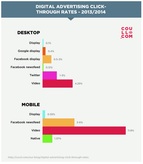
Online ads may not be as effective as their supporters claim, although mobile ads get noticed more than their desktop counterparts. Hopes for social networks profiting from selling what they know about their customers may also be dashed. Hold onto your wallet!
December 2, 2014: Smoking continues to decline, airlines crack down on Internet thieves, and email's cloudy outlook
Good news! Smoking rates continue to drop
The U.S. Centers for Disease Control's Morbidity and Mortality Weekly Report isn't what most people would consider required reading. Sometimes, however, the report can actually be downright inspirational.
For example, last week's report shows that the number of people in the U.S. who smoke cigarettes daily declined from 16.9 percent in 2005 to 13.7 percent in 2013. The number of cigarettes each person smokes per day is down as well. Mother Jones's Kevin Drum examines the smoking decline in a November 28, 2014, article.
The CDC report indicates that smoking is more prevalent among gay people than in the general population: 26 percent of gay people smoke, compared to 17 percent of all adults in the U.S. However, the CDC points out that the discrepancy could be due to the survey methodology, which relied on self-reporting and may not have accurately categorized "lesbian, gay, and bisexual."
If you're a smoker who would rather be an ex-smoker, check out the U.S. Department of Health and Human Services' Smokefree.gov, which is jam-packed with resources to help you quit. The American Cancer Society offers a Guide to Quitting Smoking.
-------------------------------------------------------------------------------------
Long arm of the law nabs 118 online credit-card thieves
It may be a drop in the bucket, but it's still reassuring to know that not all Internet criminals go unpunished. In a November 28, 2014, article on the SecurityWeek site, Eduard Kovacs reports that the recent "Global Airport Action" involving law enforcement agencies around the world led to the arrest of 118 people accused of using stolen or false credit cards to purchase airline tickets online.
The operation entailed 60 airlines operating in 45 countries, as well as the International Air Transport Association and all the major credit-card companies. The IATA estimates that the airline industry has lost $1 billion due to fraudulent online ticket purchases. Of course, those losses are passed on to us customers in the form of higher ticket prices, smaller seats, bag-check fees, and innumerable other minor indignities. So much for the friendly skies!
----------------------------------------------------------------------------
Has email use peaked?
The other day I was remarking to a friend that I'm spending much less time writing, reading, and (most importantly) deleting email than I used to. Yet reports persist that claim workers spend as much as one-fourth of their workday handling email.
Facebook co-founder Dustin Moskovitz has made it his mission to convince the world that email has peaked and will soon be obsolete. Wired's Marcus Wohlsen reports on Moskovitz's anti-email campaign in a January 21, 2014, article. Moskovitz left Facebook in 2008 and founded Asana with the goal of creating a more efficient way for workers to collaborate.
Taking the counter argument is the Atlantic's Alexis C. Madrigal, who posits in an August 14, 2014, article that email is the Internet's best feature. The reason for email overload, according to Madrigal, is that the technology is being used for purposes that it may not be well-suited to, such as document sharing and project management.
Could email evolve (or devolve) into the role for which it was conceived originally: letter writing? Imagine that!
The U.S. Centers for Disease Control's Morbidity and Mortality Weekly Report isn't what most people would consider required reading. Sometimes, however, the report can actually be downright inspirational.
For example, last week's report shows that the number of people in the U.S. who smoke cigarettes daily declined from 16.9 percent in 2005 to 13.7 percent in 2013. The number of cigarettes each person smokes per day is down as well. Mother Jones's Kevin Drum examines the smoking decline in a November 28, 2014, article.
The CDC report indicates that smoking is more prevalent among gay people than in the general population: 26 percent of gay people smoke, compared to 17 percent of all adults in the U.S. However, the CDC points out that the discrepancy could be due to the survey methodology, which relied on self-reporting and may not have accurately categorized "lesbian, gay, and bisexual."
If you're a smoker who would rather be an ex-smoker, check out the U.S. Department of Health and Human Services' Smokefree.gov, which is jam-packed with resources to help you quit. The American Cancer Society offers a Guide to Quitting Smoking.
-------------------------------------------------------------------------------------
Long arm of the law nabs 118 online credit-card thieves
It may be a drop in the bucket, but it's still reassuring to know that not all Internet criminals go unpunished. In a November 28, 2014, article on the SecurityWeek site, Eduard Kovacs reports that the recent "Global Airport Action" involving law enforcement agencies around the world led to the arrest of 118 people accused of using stolen or false credit cards to purchase airline tickets online.
The operation entailed 60 airlines operating in 45 countries, as well as the International Air Transport Association and all the major credit-card companies. The IATA estimates that the airline industry has lost $1 billion due to fraudulent online ticket purchases. Of course, those losses are passed on to us customers in the form of higher ticket prices, smaller seats, bag-check fees, and innumerable other minor indignities. So much for the friendly skies!
----------------------------------------------------------------------------
Has email use peaked?
The other day I was remarking to a friend that I'm spending much less time writing, reading, and (most importantly) deleting email than I used to. Yet reports persist that claim workers spend as much as one-fourth of their workday handling email.
Facebook co-founder Dustin Moskovitz has made it his mission to convince the world that email has peaked and will soon be obsolete. Wired's Marcus Wohlsen reports on Moskovitz's anti-email campaign in a January 21, 2014, article. Moskovitz left Facebook in 2008 and founded Asana with the goal of creating a more efficient way for workers to collaborate.
Taking the counter argument is the Atlantic's Alexis C. Madrigal, who posits in an August 14, 2014, article that email is the Internet's best feature. The reason for email overload, according to Madrigal, is that the technology is being used for purposes that it may not be well-suited to, such as document sharing and project management.
Could email evolve (or devolve) into the role for which it was conceived originally: letter writing? Imagine that!
